A) A network ACL associated with the bastion's subnet is blocking the network traffic.
B) The instance does not have a private IP address.
C) The route table associated with the bastion's subnet does not have a route to the internet gateway.
D) The security group for the instance does not have an inbound rule on port 22.
E) The security group for the instance does not have an outbound rule on port 3389.
G) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An application resides on multiple EC2 instances in public subnets in two Availability Zones. To improve security, the Information Security team has deployed an Application Load Balancer (ALB) in separate subnets and pointed the DNS at the ALB instead of the EC2 instances. After the change, traffic is not reaching the instances, and an error is being returned from the ALB. What steps must a SysOps Administrator take to resolve this issue and improve the security of the application? (Choose two.)
A) Add the EC2 instances to the ALB target group, configure the health check, and ensure that the instances report healthy.
B) Add the EC2 instances to an Auto Scaling group, configure the health check to ensure that the instances report healthy, and remove the public IPs from the instances.
C) Create a new subnet in which EC2 instances and ALB will reside to ensure that they can communicate, and remove the public IPs from the instances.
D) Change the security group for the EC2 instances to allow access from only the ALB security group, and remove the public IPs from the instances.
E) Change the security group to allow access from 0.0.0.0/0, which permits access from the ALB.
G) B) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
How can you secure data at rest on an EBS volume?
A) Encrypt the volume using the S3 server-side encryption service.
B) Attach the volume to an instance using EC2's SSL interface.
C) Create an IAM policy that restricts read and write access to the volume.
D) Write the data randomly instead of sequentially.
E) Use an encrypted file system m top of the EBS volume.
G) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which method can be used to prevent an IP address block from accessing public objects in an S3 bucket?
A) Create a bucket policy and apply it to the bucket
B) Create a NACL and attach it to the VPC of the bucket
C) Create an ACL and apply it to all objects in the bucket
D) Modify the IAM policies of any users that would access the bucket
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps Administrator receives a connection timeout error when attempting to connect to an Amazon EC2 instance from a home network using SSH. The Administrator was able to connect to this EC2 instance using from their office network in the past. What caused the connection to time out?
A) The IAM role associated with the EC2 instance does not allow SSH connections from the home network.
B) The public key used by SSH located on the Administrator's server does not have the required permissions.
C) The route table contains a route that sends 0.0.0.0/0 to the internet gateway for the VPC.
D) The security group is not allowing inbound traffic from the home network on the SSH port.
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps Administrator created an AWS CloudFormation template for the first time. The stack failed with a status of ROLLBACK_COMPLETE . The Administrator identified and resolved the template issue causing the failure. How should the Administrator continue with the stack deployment?
A) Delete the failed stack and create a new stack.
B) Execute a change set on the failed stack.
C) Perform an update-stack action on the failed stack. Perform an update-stack action on the failed stack.
D) Run a validate-template command. Run a validate-template command.
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company would like to review each change in the infrastructure before deploying updates in its AWS CloudFormation stacks. Which action will allow an Administrator to understand the impact of these changes before implementation?
A) Implement a blue/green strategy using AWS Elastic Beanstalk.
B) Perform a canary deployment using Application Load Balancers and target groups.
C) Create a change set for the running stack.
D) Submit the update using the UpdateStack API call.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps Administrator is responsible for maintaining an Amazon EC2 instance that acts as a bastion host. The Administrator can successfully connect to the instance using SSH, but attempts to ping the instance result in a timeout. What is one reason for the issue?
A) The instance does not have an Elastic IP address
B) The instance has a security group that does not allow Internet Control Message Protocol (ICMP) traffic
C) The instance is not set up in a VPC using AWS Direct Connect
D) The instance is running in a peered VPC
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps Administrator stores crash dump files in Amazon S3. New security and privacy measures require that crash dumps older than 6 months be deleted. Which approach meets this requirement?
A) Use Amazon CloudWatch Events to delete objects older than 6 months.
B) Implement lifecycle policies to delete objects older than 6 months.
C) Use the Amazon S3 Standard-Infrequent Access (S3 Standard-IA) storage class to automatically delete objects older than 6 months.
D) Create versioning rules to delete objects older than 6 months.
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A storage admin wants to encrypt all the objects stored in S3 using server side encryption. The user does not want to use the AES 256 encryption key provided by S3. How can the user achieve this?
A) The admin should upload his secret key to the AWS console and let S3 decrypt the objects
B) The admin should use CLI or API to upload the encryption key to the S3 bucket. When making a call to the S3 API mention the encryption key URL in each request
C) S3 does not support client supplied encryption keys for server side encryption
D) The admin should send the keys and encryption algorithm with each API call
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company's customers are reporting increased latency while accessing static web content from Amazon S3. A SysOps Administrator observed a very high rate of read operations on a particular S3 bucket. What will minimize latency by reducing load on the S3 bucket?
A) Migrate the S3 bucket to a region that is closer to end users' geographic locations.
B) Use cross-region replication to replicate all of the data to another region.
C) Create an Amazon CloudFront distribution with the S3 bucket as the origin.
D) Use Amazon ElastiCache to cache data being served from Amazon S3.
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps Administrator implemented the following bucket policy to allow only the corporate IP address range of 54.240.143.0/24 to access objects in an Amazon S3 bucket. 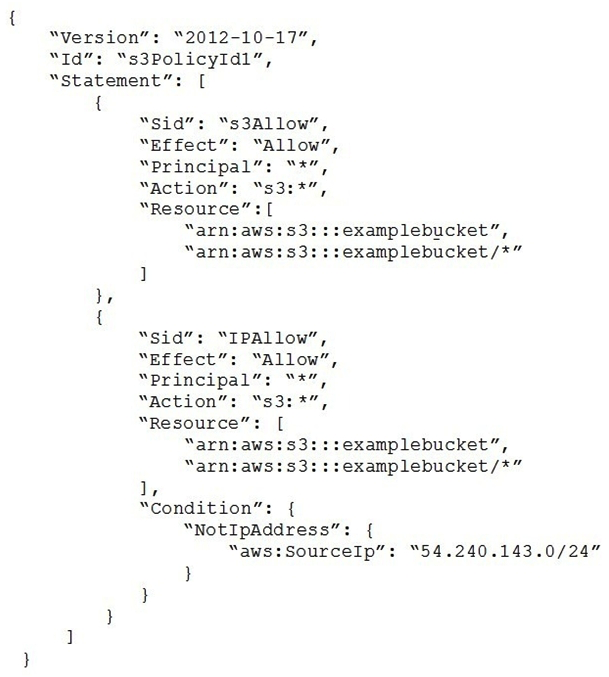 Some employees are reporting that they are able to access the S3 bucket from IP addresses outside the corporate IP address range. How can the Administrator address this issue?
Some employees are reporting that they are able to access the S3 bucket from IP addresses outside the corporate IP address range. How can the Administrator address this issue?
A) Modify the Condition operator to include both NotIpAddress and IpAddress to prevent unauthorized access to the S3 bucket. Modify the Condition operator to include both NotIpAddress and IpAddress to prevent unauthorized access to the S3 bucket.
B) Modify the Condition element from the IAM policy to aws:StringEquals instead of aws:SourceIp . element from the IAM policy to aws:StringEquals instead of aws:SourceIp .
C) Modify the IAM policy instead of the bucket policy to restrict users from accessing the bucket based on their source IP addresses.
D) Change Effect from Allow to Deny in the second statement of the policy to deny requests not from the source IP range. Change Effect from Allow to Deny in the second statement of the policy to deny requests not from the source IP range.
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps administrator is implementing automated I/O load performance testing as part of the continuous integration/continuous delivery (CI/CD) process for an application. The application uses an Amazon Elastic Block Store (Amazon EBS) Provisioned IOPS volume for each instance that is restored from a snapshot and requires consistent I/O performance. During the initial tests, the I/O performance results are sporadic. The SysOps administrator must ensure that the tests yield more consistent results. Which actions could the SysOps administrator take to accomplish this goal? (Choose two.)
A) Restore the EBS volume from the snapshot with fast snapshot restore enabled.
B) Restore the EBS volume from the snapshot using the cold HDD volume type.
C) Restore the EBS volume from the snapshot and pre-warm the volume by reading all of the blocks.
D) Restore the EBS volume from the snapshot and configure encryption.
E) Restore the EBS volume from the snapshot and configure I/O block size at random.
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company's customers are reporting increased latency while accessing static web content from Amazon S3. A SysOps Administrator observed a very high rate of read operations on a particular S3 bucket. What will minimize latency by reducing load on the S3 bucket?
A) Migrate the S3 bucket to a region that is closer to end users' geographic locations.
B) Use cross-regions replication to replicate all of the data to another region.
C) Create an Amazon CloudFront distribution with the S3 bucket as the origin.
D) Use Amazon ElasticCache to cache data being served from Amazon S3.
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which of the following requires a custom CloudWatch metric to monitor?
A) Data transfer of an EC2 instance
B) Disk usage activity of an EC2 instance
C) Memory Utilization of an EC2 instance
D) CPU Utilization of an EC2 instance
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A user has setup a VPC with CIDR 20.0.0.0/16. The VPC has a private subnet (20.0.1.0/24. and a public subnet (20.0.0.0/24.. The user's data center has CIDR of 20.0.54.0/24 and 20.1.0.0/24. If the private subnet wants to communicate with the data center, what will happen?
A) It will allow traffic communication on both the CIDRs of the data center
B) It will not allow traffic with data center on CIDR 20.1.0.0/24 but allows traffic communication on 20.0.54.0/24
C) It will not allow traffic communication on any of the data center CIDRs
D) It will allow traffic with data center on CIDR 20.1.0.0/24 but does not allow on 20.0.54.0/24
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A SysOps Administrator is receiving alerts related to high CPU utilization of a Memcached-based Amazon ElastiCache cluster. Which remediation steps should be taken to resolve this issue? (Choose two.)
A) Add a larger Amazon EBS volume to the ElastiCache cluster nodes
B) Add a load balancer to route traffic to the ElastiCache cluster
C) Add additional worker nodes to the ElastiCache cluster
D) Create an Auto Scaling group to the ElastiCache cluster
E) Vertically scale the ElastiCache cluster by changing the node type
G) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Content Processing team has notified a SysOps Administrator that their content is sometimes taking a long time to process, whereas other times it processes quickly. The Content Processing submits messages to an Amazon Simple Queue Service (Amazon SQS) queue, which details the files that need to be processed. An Amazon EC2 instance polls the queue to determine which file to process next. How could the Administrator maintain a fast but cost-effective processing time?
A) Attach an Auto Scaling policy to the Amazon SQS queue to increase the number of EC2 instances based on the depth of the SQS queue
B) Create an Auto Scaling policy to increase the number of EC2 instances polling the queue and a CloudWatch alarm to scale based on MaxVisibility Timeout
C) Attach an Auto Scaling policy to the SQS queue to scale instances based on the depth of the dead-letter queue
D) Create an Auto Scaling policy to increase the number of EC2 instances polling the queue and a CloudWatch alarm to scale based on ApproximateNumberOfMessagesVisible
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A custom application must be installed on all Amazon EC2 instances. The application is small, updated frequently and can be installed automatically. How can the application be deployed on new EC2 instances?
A) Launch a script that downloads and installs the application using the Amazon EC2 user data.
B) Create a custom API using Amazon API Gateway to call an installation executable from an AWS CloudFormation Template.
C) Use AWS Systems Manager to inject the application into an AMI.
D) Configure AWS CodePipeline to deploy code changes and updates.
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company has attached the following policy to an IAM user. 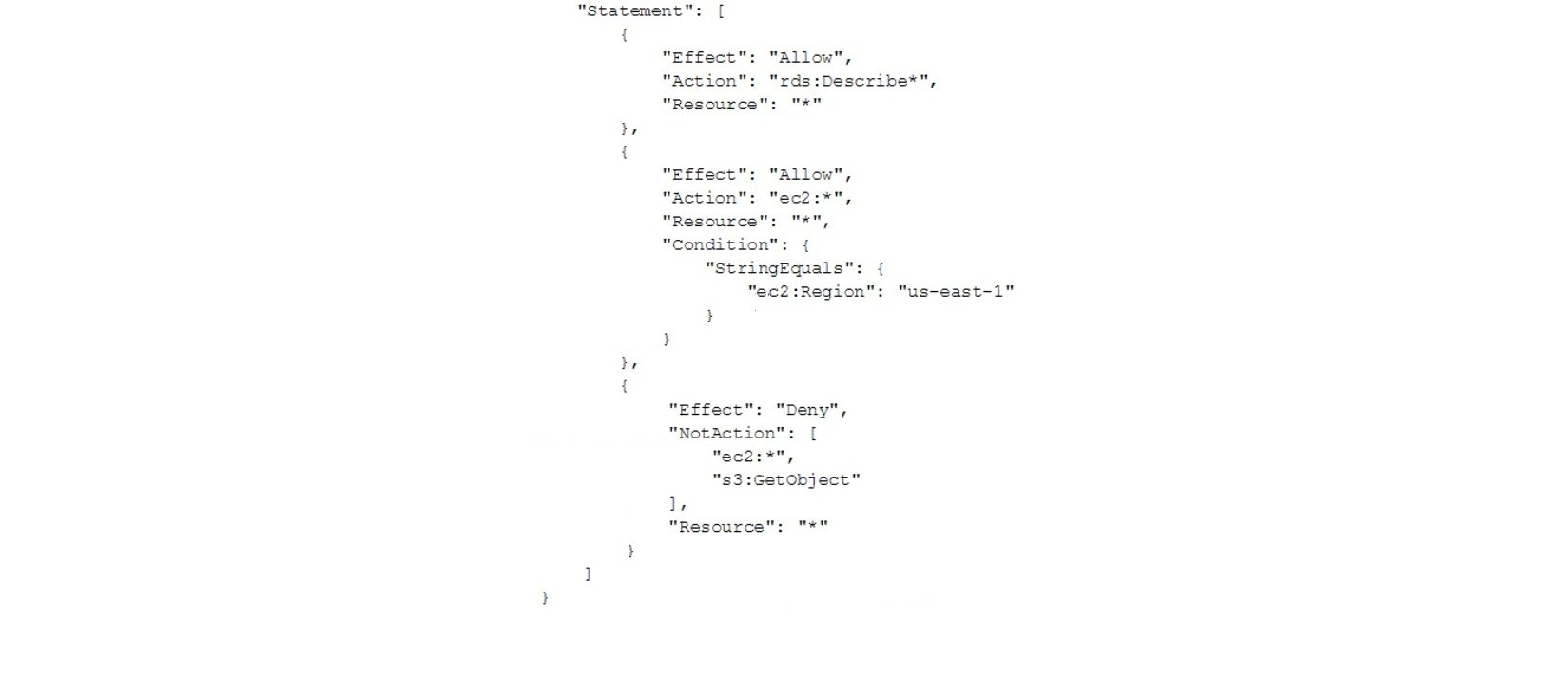 Which of the following actions are allowed for the IAM user?
Which of the following actions are allowed for the IAM user?
A) Amazon RDS DescribeDBInstances action in the us-east-1 Region Amazon RDS DescribeDBInstances action in the us-east-1 Region
B) Amazon S3 PutObject operation in a bucket named testbucket Amazon S3 PutObject operation in a bucket named testbucket
C) Amazon EC2 DescribeInstances action in the us-east-1 Region Amazon EC2 DescribeInstances action in the us-east-1 Region
D) Amazon EC2 AttachNetworkInterface action in the eu-west-1 Region AttachNetworkInterface action in the eu-west-1 Region
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Showing 561 - 580 of 976
Related Exams